Don't Let Weak Third-Party Risk Management Take Down Your Business
- With businesses increasingly relying on external entities to fulfill various operational needs, robust third-party risk management (TPRM) has become essential.
- Robust TPRM includes prioritizing vendors, leveraging technology, going beyond cybersecurity and involving procurement partners.
- AI-driven procurement software can boost your risk management strategies.
June 12, 2023 | Risk Management 3 minutes read
Effective management of third-party risks has emerged as a critical priority for organizations seeking to safeguard their operations and mitigate potential threats.
With businesses increasingly relying on external entities to fulfill various operational needs, ensuring the absence of risks associated with these third parties have become a complex and pressing task.
Consequently, organizations are devoting significant time and resources towards developing meticulous standards and assessments for potential third-party vendors. This proactive approach serves the dual purpose of mitigating risks within the supply chain network and bolstering overall security measures.
This blog explores key strategies and considerations for improving risk mitigation capabilities and building strong supplier relationships.
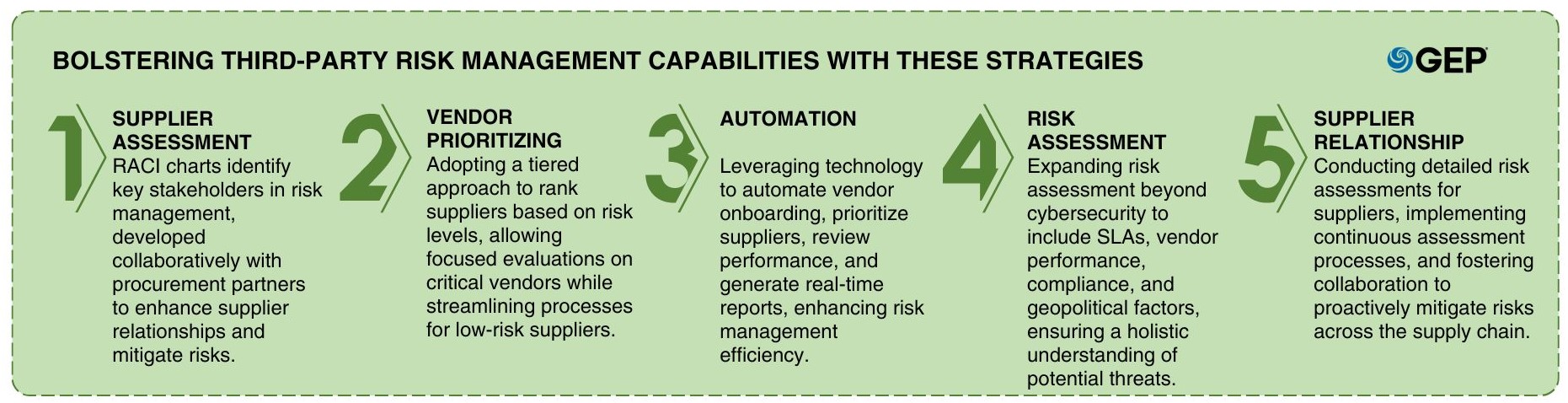
1. Assessment Capabilities, RACI Charts and Supplier Relationships
RACI charts are the first step towards risk management because they identify the ‘Responsible, Accountable, Consulted, and Informed’ individuals or departments in context to the different risks in procurement.
These RACI charts must be developed through the joint effort of a company’s internal stakeholders and procurement partners. Procurement partners also help manage relationships with suppliers and vendors, making long-term risk management easier and improving risk mitigation capabilities.
2. Prioritizing Vendors: A Risk-Based Approach
To efficiently manage third-party risks, organizations should rank suppliers based on risk levels.
Tier 1: These are strategic and critical vendors who may expose the businesses to high risk. Here, rigorous evaluations, including site visits, should be conducted.
Tier 2: These suppliers may expose businesses to medium-level risk.
Tier 3: These are low-risk suppliers; they are also easily replaceable.
3. Leveraging Automation for Efficiency
Automation plays a crucial role in enhancing risk management efficiency. Businesses should leverage technology to automate routine tasks and save resources. Automation can be applied in areas such as:
Vendor onboarding: Streamlining the onboarding process through automated workflows and document management.
Prioritizing vendors/suppliers: Utilizing automated systems to assess and prioritize vendors based on predefined criteria.
Reviewing supplier performance: Automating the evaluation of supplier performance through data analysis and key performance indicators.
Reporting: Generating custom reports automatically to provide real-time insights into risk management activities.
4. Expanding Risk Assessment Beyond Cybersecurity
While cybersecurity is a critical aspect of risk management, businesses should also consider other risks that impact their operations. These risks may include service level agreements (SLAs), vendor performance, supplier creditworthiness, compliance, logistics, financial stability, weather-related factors and geopolitical risks. A comprehensive approach to risk assessment ensures a holistic understanding of potential threats and effective mitigation strategies.
Watch: How To Create a Definitive Third Party Risk Management Program Once And For All
5. Managing Supplier Relationships for Effective Risk Mitigation
Effective supplier management is essential for mitigating risks. Organizations should gather relevant information from their supply chain and develop risk heat maps to visualize the impact and likelihood of different risk categories. Key steps include:
- Conducting detailed risk assessments for each supplier, looking at factors such as adverse news/events, geopolitical risks, ESG risks, modern slavery, corruption and sanctions.
- Implementing a continuous assessment process that utilizes real-time data to promptly adapt to changes in the supply chain.
- Fostering collaboration and communication with suppliers to establish a proactive risk mitigation approach and address potential issues in a timely manner.
6. Harnessing Data and Technology for Risk Management
Post defining and evaluating risks, you must start with active risk mitigation operations. Businesses must leverage available data and adopt technology resources to strengthen these risk management efforts.
The latest AI-powered procurement platforms can automate multiple statutory risk mitigation processes and efficiently spot short-and-long-term risks. Additionally, human analysis and market intelligence based on the continuous incoming data from various SMEs and reliable sources help the responsible stakeholders expand the scope of risk management and boost risk mitigation efforts.
7. Engaging Internal Stakeholders and Procurement Partners
Internal stakeholders and procurement partners contribute significantly towards effective risk management. While procurement partners offer expertise and technology to streamline operations, the final decision-making authority lies with the company’s decision-makers. Collaboration between internal stakeholders and procurement partners is vital for strategic operations, including supplier relationships, risk identification, spend analysis, and strategy-building.
To Sum Up
Implementing robust third-party risk management protocols is critical for organizations to navigate the complexities of today’s business environment. By prioritizing vendors, leveraging automation, expanding risk assessment beyond cybersecurity, and involving internal stakeholders and procurement partners, businesses can strengthen their risk mitigation capabilities and protect their procurement and supply chain operations.