How to Eliminate Banking Fraud with Secure Procure-to-Pay Systems
- Banking fraud in procurement exploits the gaps between approvals, the lag between data entry and verification and the blind spots in disconnected P2P platforms.
- Secure procure-to-pay systems eliminate fraudulent transactions by building automated checks, segregation of duties and real-time anomaly detection directly into the payment workflow.
- Predictive fraud intelligence is rapidly becoming a requirement for organizations serious about securing their financial operations.
May 04, 2026 | Procurement Software 4 minutes read
The invoice looked legitimate. The vendor was in the system. The bank details had been “updated” three days earlier.
This is how most procurement fraud actually happens: not through perimeter breaches but through deliberate exploitation of process gaps. The time between a vendor record change and the next payment run. Or the approval that gets rubber-stamped under volume pressure. The duplicate invoice that slips through because the PO matching wasn’t quite right.
Secure procure-to-pay (P2P) systems exist specifically to close these gaps. Understanding how to eliminate banking fraud starts with knowing where the vulnerabilities live in the P2P process and what a genuinely secure P2P platform does differently.
Why Does Procure-to-Pay Matter for Fraud Prevention?
The procure-to-pay process controls the full lifecycle of organizational spending: from purchase requisition to the final payment instruction sent to a bank. That makes it both the primary target for financial fraud and the most effective place to prevent it.
Fraud risk concentrates at three specific points: vendor master data management (where fraudulent payees get added or legitimate bank details get changed), the three-way match process (where invoices, POs and receipts are reconciled) and the payment approval workflow (where authorization controls can be bypassed). Organizations using manual processes or fragmented P2P payment platforms carry structural vulnerability at all three simultaneously.
The fundamental insight of secure P2P design is this: fraud prevention isn’t a layer you add on top of a payment system. It’s an architectural property of the system itself.
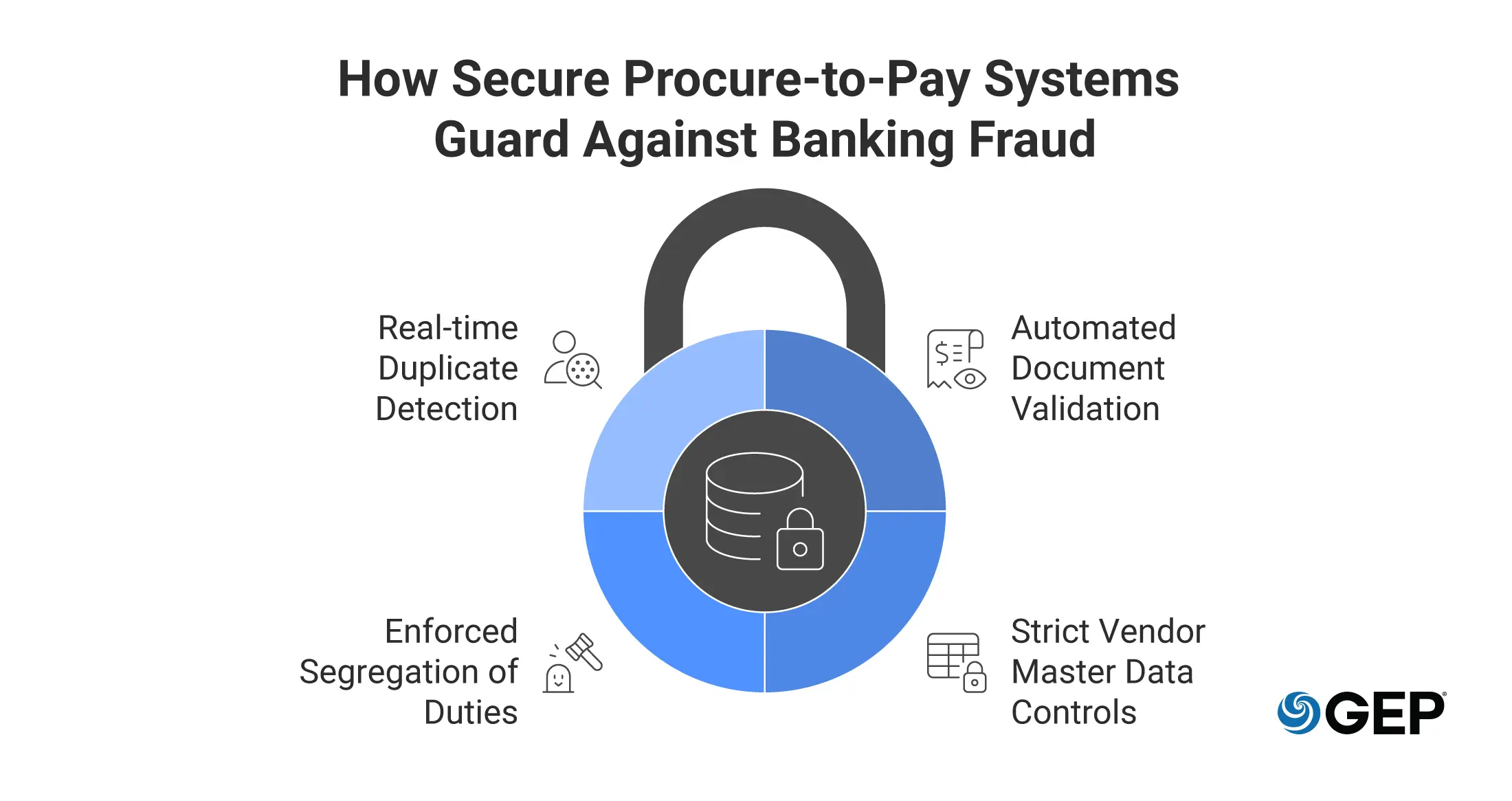
How Secure Procure-to-Pay Systems Help Eliminate Banking Fraud
Automated document validation
Helps you fight fraud at the point of entry. Intelligent invoice processing cross-references invoice data against purchase orders, goods receipts and vendor master records in real time, flagging discrepancies before funds leave the building.
Strict vendor master data controls
Payment diversion fraud most commonly enters through unauthorized changes to vendor banking details. Secure P2P systems enforce dual authorization for any banking detail modification, create a full audit trail of changes and trigger independent verification workflows before any modified detail is activated.
Enforced segregation of duties
The ability to both approve a payment and initiate the underlying transaction is a control failure. Secure platforms enforce role-based access controls that make it impossible for the same individual to request, approve and execute a payment.
Real-time duplicate detection
Duplicate invoice submission is among the most common forms of P2P payment fraud. AI-native matching identifies near-duplicate invoices with slightly varied numbers, dates or amounts, catching what rule-based systems routinely miss.
Best Practices for Implementing Secure Procure-to-Pay Systems
Conduct a fraud risk assessment first
Map your current P2P process against known fraud vectors to identify where your specific vulnerabilities lie. A company with 500 active vendors faces different exposure than one managing 50,000 vendor relationships across multiple geographies.
Establish clear payment authority matrices
Define precisely who can approve payments at which thresholds and build those limits into the platform as enforced system rules, not guidelines.
Train the human layer
Technology controls fail when people override them under pressure or don’t recognize what fraud looks like. Regular training on social engineering tactics, particularly business email compromise schemes targeting AP teams, is a necessary complement to platform controls.
Driving Operational Excellence Through Predictive Fraud Intelligence
The most sophisticated secure procure-to-pay systems have moved from reactive fraud detection to predictive fraud intelligence: identifying risk before it crystallizes. Machine learning models identify transactions that deviate from established behavioral norms, even when they technically comply with every defined rule.
This matters because sophisticated fraudsters design schemes specifically to stay within rule-based thresholds: splitting large payments to fall below approval limits, timing submissions during high-volume periods, using legitimate-looking vendor identities established months before the fraud executes. Predictive intelligence sees through these patterns in ways that static rules cannot.
Fix Fragmented P2P Workflows
See How AI-Native Source-to-Pay Technology Turns Silos Into an Orchestrated Operation
Why Secure Procure-to-Pay Systems Are a Financial Imperative
Banking fraud in procurement is a reality that every organization managing significant payment volumes will encounter. How quickly can you deploy a secure P2P system before the next attempt succeeds?
The organizations eliminating fraudulent transactions most effectively treat fraud prevention as a core architectural requirement of their P2P platform. They build automated controls into the workflow itself, enforce governance through technology and continuously improve their defenses using behavioral analytics that evolve faster than fraud schemes.
The result is a more efficient, more auditable financial operation that finance leadership can confidently stand behind. Use secure payment systems built into an integrated procure-to-pay platform to establish the controls your organization needs.
Frequently Asked Questions (FAQ)
How do you assess fraud risk in the procure-to-pay process?
A P2P fraud risk assessment maps each stage of the lifecycle against known vectors: unauthorized vendor creation, banking detail manipulation, invoice tampering, duplicate billing and unauthorized payment approval. Prioritize vendors and transaction types with the highest value, highest frequency or most complex approval pathways as your areas of greatest exposure.
What are the most common “red flags” of P2P payment fraud in 2026?
The highest-frequency red flags include vendor bank detail changes shortly before a payment run, invoices from email domains that don’t match established vendor contacts, payments to new vendors above threshold without a matching PO, invoice amounts just below authorization limits and sudden spikes in submission frequency from existing vendors. Most of these patterns are only detectable at scale through behavioral analytics.
What role does governance and internal control play in preventing P2P fraud?
Without strong governance, even the best platform can be undermined. Effective P2P fraud governance defines who can perform what actions at which thresholds, ensures audit functions are independent from payment execution, requires periodic vendor master re-verification and creates escalation paths for exception handling that don’t route around core controls.